| Terminology | Definition | Elaboration/Exemplification |
|---|---|---|
| Risk | Risk is a situation involving exposure to danger of any aspect. It is a real or perceived threat against any aspect of life. |  |
| Resilience | It denotes the ability to recover quickly from difficulties and bounce back to normal state. | |
| Cybersecurity | Cybersecurity is the practice of protecting electronic data, systems, networks, and programs from digital attacks and unauthorized assess. Cyberattacks are usually aimed at accessing, changing, or destroying sensitive information; extorting money from users; or interrupting normal business processes, know as cybercrime. | Read five easy steps to stop hackers |
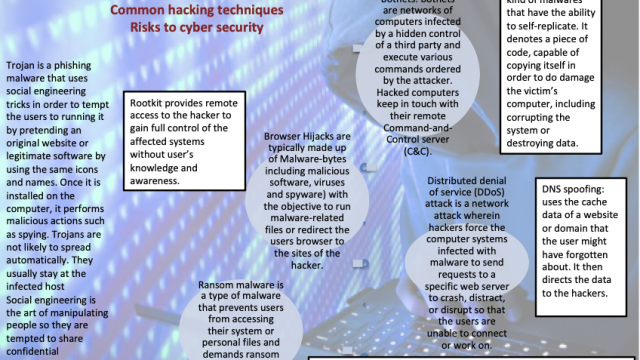
| Different types of cyber attacks (risk to ICT) HACKING | It simply refers to gaining of unauthorized access to data in a system or computer. This is done through cracking of passwords and codes which gives access to the systems. Cracking is the term which specifies the method by which the password or code is obtained (password cracking algorithms programs). The person who undertakes hacking is known as the hacker. | Common hacking techniques include: Botnets Browser hijacks Denial of service (DoS) Ransomware Rootkits Trojans and other Viruses Worms DNS spoofing (Refer to the schematic for more information) |
| Phishing | It is a type of hacking. Phishing attacks are the practice of sending fraudulent communications that appear to come from a reputable source. It is usually done through email. The goal is to steal sensitive data like credit card and login information, or to install malware or hacking software on the victim’s machine. | Click here to read how to tackle phishing |
| Resilience: Virtual Private Networks (VPNs) | It is a security mechanisms and a protocol by which corporate networks connect to offsite and remote locations by using encrypted data and tunneling protocols. VPN allow the users to securely access a network from different locations via a public telecommunications network, most frequently the Internet. securely cover the transmitting and receiving IP addresses thereby preventing hackers from making unauthorized encroachment. Furthermore, data transmission over this tunnel is subjected to a very high level of encryption thereby preventing leakage. | The key VPN advantage is that it is less expensive than a private wide area network (WAN). In a remote-access VPN, an organization uses an outside enterprise service provider (ESP) to establish a network access server (NAS). Remote users then receive VPN desktop software and connect to the NAS via a toll-free number, which accesses the organization's network (source: techopedia) |
A few of the actions to increase resilience as suggested by Symantec are as follows:
- Risk Profiling – Identify the risk profile based on the exposure.
- Risk Reduction – Formulate risk reduction initiatives ( Risk Management, Data encryption etc.)
- Awareness – Make the stakeholders part of cyber resilience (Educate employees, supply chain)
- Strategic approach in maintaining cyber standard – Applying cyber resilience methods as a long term strategic and competitive advantage. Engage Security Vendors such as cyber security farm, VPN etc.
Apple Inc. will bring hundreds of billions of overseas dollars back to the U.S., pay about $38 billion in taxes on the money and invest tens of billions on domestic jobs, manufacturing and data centers in the coming years. Read Fortune article on re-shoring of apple.
Important Case Studies from Unit 6
Disruptive Technology : Drone
Cyber crime resilience : Role of VPN and Electronic passport
Case study of Trans-boundary pollution – Gulf Oil spill (2010) and Chernobyl nuclear disaster
Case of profit repatriation by one TNC
One geopolitical conflict and it’s global impact – Middle East tension and Syrian Crisis